If the score is below that of your opponents, getting measures to secure your IP footprint will let you become a additional eye-catching option to potential clients. Once your Firm’s security score exceeds that of your competitors, you've a possibility to leverage that in small business negotiations.
Cybercriminals exploit vulnerabilities in facts-pushed applications to insert malicious code into a databased by way of a destructive SQL statement. This provides them usage of the delicate data contained in the database.
So, how can malicious actors achieve Charge of Pc devices? Here are some frequent approaches accustomed to threaten cyber-safety:
We use cookies to help make your knowledge of our Internet sites improved. By utilizing and further more navigating this website you acknowledge this. In depth information regarding the usage of cookies on this Web-site is accessible by clicking on more information.
紧密集成的产品套件,赋能任意规模安全团队跨企业网络快速检测、调查和响应各类安全威胁。
Stability questionnaires: The UpGuard System will help safety teams scale their stability questionnaire approach by 10x by its sector-top questionnaire library and flexible questionnaire templates.
A TPRM committee is vital to building a culture of protection consciousness and efficiently identifying, assessing, and mitigating threats connected to 3rd-get together relationships.
A third party seller danger management plan can be a structured, company-vast approach to determining, examining, mitigating, and consistently monitoring the hazards posed by exterior vendors and suppliers. Compared with casual procedures — which could be scattered throughout departments or groups — a formal TPRM plan gives consistent governance, standardized policies, distinct roles, and committed instruments.
Designed particularly for making seller hazard management uncomplicated but strong, Isora will help ensure that your TPRM software scales easily alongside your Business for peace of mind without additional complexity.
Arrange a 3rd-bash risk assessment management technique to trace possibility evaluation development and catalog safety questionnaires.
The importance of method monitoring is echoed inside the “10 methods to cyber safety”, steerage provided by Scoring the U.
Digital protection protocols also target actual-time malware detection. Numerous use heuristic and behavioral analysis to monitor the behavior of the software and its code to defend against viruses or Trojans that improve their condition with Just about every execution (polymorphic and metamorphic malware).
Tightly integrated merchandise suite that allows protection groups of any measurement to speedily detect, look into and respond to threats over the company.
For some, the most effective place to start out will probably be being familiar with the difference between a TPRM system as well as a TPRM program. Gauging the place your organization lands about the spectrum of TPRM maturity might help slim concentrate on wherever there’s room to improve.
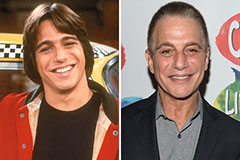 Tony Danza Then & Now!
Tony Danza Then & Now!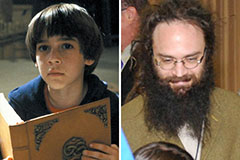 Barret Oliver Then & Now!
Barret Oliver Then & Now! Shane West Then & Now!
Shane West Then & Now! Earvin Johnson III Then & Now!
Earvin Johnson III Then & Now! Lucy Lawless Then & Now!
Lucy Lawless Then & Now!